Quantum computing is beginning to shape enterprise strategy, not because of its current capabilities, but because of the future risks and opportunities it presents. Although the timeline for scalable, fault-tolerant quantum machines remains uncertain, business and technology leaders are already encountering implications that warrant structured attention. These include questions of cryptographic resilience, regulatory alignment, long-term data security and architectural design. The conversation is moving beyond technical experimentation.
Governments are developing national strategies, regulators are issuing guidance and early pilots are underway across multiple sectors. The challenge for most enterprises is not whether to engage with quantum computing but how to prepare for its eventual impact, without overcommitting or underestimating the stakes.
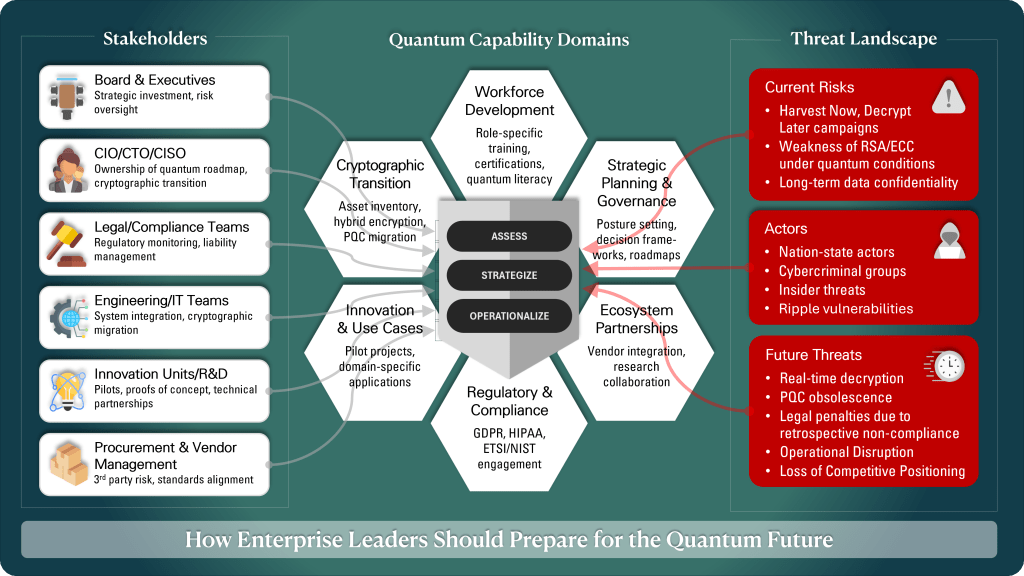
In my recently published whitepaper, Quantum readiness — Strategic imperatives for enterprise organizations, I proposed that readiness should be treated as a strategic discipline anchored in six capability domains, supported by a phased implementation model. Before turning to that framework, it is necessary to clarify why quantum readiness is already relevant and what distinguishes it from typical emerging technology planning.
Why quantum readiness now?
Quantum computing often appears on horizon scans but rarely on board-level agendas. This is not due to a lack of potential, but because the risk timeline is widely misunderstood. The most immediate concern is not whether organizations can run quantum applications, but whether their current systems and controls can survive a world where adversaries can. In particular, the integrity of widely used cryptographic protocols such as RSA and ECC is at stake. Quantum algorithms like Shor’s can break the mathematical foundations of public key encryption.
While the hardware needed to scale these algorithms is still in development, harvesting of encrypted data is already underway, with threat actors fully expecting to decrypt it later. This “harvest now, decrypt later” model creates a lagging risk exposure, especially for sensitive information with long confidentiality requirements. In practice, this means quantum computing creates a current vulnerability rather than a purely future one. Data protected today may be compromised tomorrow if transition planning is delayed.
Regulatory institutions have recognised this. NIST has finalised its first set of quantum-safe encryption algorithms, and ETSI has issued technical migration guidance. These efforts signal a shift from research to operational expectations.
There is also a more general compliance dimension. Legal regimes like GDPR or HIPAA require that current encryption techniques be robust. If those techniques fail, enterprises may be held liable downstream for using obsolete controls. National strategies, like the UK’s call for early private-sector engagement, are also being adopted. The goal is not only to defend against quantum threats but also to participate in shaping the ecosystem and standards landscape. In my whitepaper, I argued that readiness should not be equated with premature implementation. Rather, it involves institutionalising foresight, creating adaptive governance and building capability before external pressure forces reactive action.
Antony Panteli
The 6 strategic domains of quantum readiness
Organizations seeking to mitigate quantum-induced risk and exploit emerging opportunities must act across six interrelated capability areas.
1. Cryptographic transition
Quantum computing undermines the foundation of widely used encryption protocols. RSA, ECC and other public key systems rely on mathematical problems that quantum algorithms like Shor’s can solve efficiently. Migration to post-quantum cryptography (PQC) is not optional. It is an emerging compliance requirement and a prerequisite for sustainable security architecture. Preparation begins with a cryptographic asset inventory to identify exposure points.
This should cover internal systems, cloud services, supply chain interfaces and data in transit. Hybrid encryption models, which combine classical and post-quantum cryptography (PQC) schemes, can serve as interim solutions while standards mature. Governance functions must adapt by embedding quantum risk into enterprise risk registers, policy documentation and cybersecurity audits.
2. Workforce capability
Quantum readiness requires informed leadership and cross-functional literacy. Many executive teams lack a shared understanding of quantum risks and potential applications. Without this, strategic planning becomes fragmented or delayed. Targeted education programmes for boards, legal teams, risk officers and engineers are essential. Skill development should correspond to role-specific needs. Engineers need training in cryptographic migration and hybrid implementation. Legal and compliance professionals must stay current with the evolving policy landscapes. Executives require context to inform investment decisions and drive governance reforms. Upskilling through academic partnerships or external certifications maintains capability as the field changes.
3. Strategic planning and governance
Quantum readiness introduces a planning challenge not typically found in conventional technology initiatives. The development timeline is uncertain, impacts vary by sector and regulation is in flux. Effective governance requires organizations to define a posture. This might be observational, exploratory or proactive. The selected posture must then be embedded into strategic planning and decision-making frameworks. Planning should distinguish between short-term preparatory actions and longer-term integration.
For example, cryptographic migration, workforce education and pilot testing may occur in the near term. System redesign and regulatory adaptation may take longer to implement. Enterprise governance boards, risk committees and investment processes should be aligned to review progress and adjust priorities as external conditions shift.
4. Regulatory engagement
Quantum computing has implications for compliance frameworks. Laws such as GDPR and HIPAA assume that data protected by today’s encryption will remain secure over time. If these assumptions no longer hold, compliance risks will emerge even in the absence of misconduct. Regulatory expectations are evolving. NIST and ETSI have introduced post-quantum cryptographic standards, and national strategies are increasingly calling on businesses to assess their readiness. Organizations must assess their regulatory exposure, especially for long-retention data or cross-border data flows. Procurement processes, vendor contracts and internal audit frameworks should be reviewed to ensure they reflect updated expectations. Legal and compliance teams should actively monitor regulatory consultations and prepare to respond to emerging obligations.
5. Innovation opportunity
Quantum computing also presents an opportunity for strategic differentiation. Unlike general-purpose technologies, quantum tools are likely to offer a domain-specific advantage first. Applications such as portfolio optimisation, molecular simulation and fraud detection could benefit from early experimentation.
Innovation teams should identify internal problems that align with quantum strengths. These may include optimisation bottlenecks, complex simulations or probabilistic modelling requirements. Feasibility studies, sandboxed pilots and collaboration with cloud-based quantum providers can support practical exploration. Where early results show promise, organizations can begin defining integration pathways, measuring impact and building internal fluency in quantum methods.
6. Ecosystem partnerships
Quantum technologies are evolving across a fragmented landscape. No single organization is likely to master hardware, software and standards independently. Strategic partnerships with technology vendors, research institutions, policymakers and industry consortia are necessary to access capabilities, influence standards and reduce risk. Partnerships should be goal-oriented. These might include testing infrastructure access, collaborating on proofs of concept or contributing to post-quantum encryption initiatives. Internally, governance models must be capable of managing external engagements. This includes intellectual property management, compliance alignment and investment oversight. Organizations that structure partnerships effectively will be better positioned to adapt to external shifts and participate in the broader evolution of the quantum ecosystem.
| Capability domain | Core focus | organizational implications |
| Cybersecurity and cryptographic transition | Safeguarding data through cryptographic assessment and migration to post-quantum standards | Enables continued data protection, supports regulatory alignment and mitigates long-term decryption risks |
| Workforce and skills development | Building internal understanding and role-specific quantum literacy | Equips teams to evaluate quantum risks and opportunities, reducing reliance on external expertise |
| Strategic roadmap and governance alignment | Embedding quantum into enterprise planning and decision-making | Ensures leadership alignment, phased execution and organizational accountability for quantum engagement |
| Regulatory and compliance frameworks | Managing emerging legal, regulatory and contractual risks | Protects compliance posture, supports proactive disclosure and aligns with evolving policy environments |
| Innovation and use case acceleration | Identifying, piloting and validating quantum-relevant applications | Enables structured experimentation, supports value measurement and guides investment in high-impact use cases |
| Ecosystem partnerships | Access capability and shape standards through external relationships. | Provides early access, mitigates uncertainty and secures strategic influence in a fragmented innovation landscape. |
From strategy to execution: A phased model
To convert strategy into action, organizations can adopt a three-phase model: Assess, strategize and operationalize. This structure supports proportionate investment while preserving flexibility.
Phase 1: Assess
Establishing a baseline understanding.
- Inventory cryptographic assets and classify by sensitivity and exposure
- Deliver executive briefings to build organizational awareness
- Evaluate workforce capability and identify gaps
- Monitor developments in hardware, policy and standards
The outcome of this phase is a clear understanding of risk, dependencies and internal readiness.
Phase 2: strategize
This phase focuses on aligning internal posture and defining forward motion.
- Determine strategic posture and define engagement priorities
- Identify quantum-relevant use cases with potential impact
- Draft a roadmap that distinguishes short, medium and long-term actions
- Establish governance structures and cross-functional alignment
The strategy should be pragmatic, resource-aware and periodically reviewed considering new developments.
Phase 3: operationalize
The final phase involves execution and capability development.
- Launch pilot projects and feasibility studies
- Initiate post-quantum cryptographic migration in priority areas
- Deliver role-specific training and certification programmes
- Integrate quantum considerations into governance and reporting structures
Progress should be tracked against defined criteria, including risk reduction, knowledge improvement and compliance alignment. Roadmaps should remain adaptable.
| Phase | Primary objective | Key activities | outcomes |
| Assess | Establish baseline readiness and risk exposure | -Conduct cryptographic asset inventory -Deliver executive briefings -Evaluate workforce awareness -Monitor market and policy signals |
Shared organizational understanding of quantum risks, dependencies and capability gaps |
| Strategize | Define engagement posture and identify areas of opportunity | -Determine strategic focus and posture -Identify quantum-relevant use cases -Draft roadmap -Align internal stakeholders |
Coherent quantum strategy aligned to business priorities, with cross-functional sponsorship |
| Operationalize | Execute pilots and build operational capability | -Launch PoCs with partners -Begin cryptographic migration planning -Deliver training -Integrate quantum into governance structures |
Measurable activity, operational frameworks and internal capability to manage quantum impact |
Integrating capability domains across the implementation lifecycle
The six capability domains are not abstract or stand-alone constructs. They serve as the operational enablers for each stage of the quantum readiness journey. Without structured investment in these areas, organizations will lack the skills, processes and governance capacity required to execute a phased implementation with credibility or resilience.
- During the Assess phase, readiness is dependent on visibility. Internal cybersecurity expertise and tools are necessary to identify and categorise cryptographic assets for comprehensive reviews. Similarly, the maturity of workforce development structures and compliance frameworks is related to assessing workforce knowledge and scanning regulatory dependencies. In areas where these domains are absent or underdeveloped, assessment is superficial and disconnected from action.
- The Strategize phase requires organizations to make informed choices. Roadmap planning, posture definition and prioritisation of quantum use cases depend on input from governance, innovation and regulatory functions. These, in turn, must be grounded in strong domain capability. For instance, planning a cryptographic transition without established cryptographic lifecycle management or vendor-aligned architecture models creates incoherence and risk.
- The Operationalize phase is only feasible where core capabilities are active. Executing pilots requires innovation partnerships, internal skills and evaluation protocols. Delivering training depends on the readiness of the workforce. Embedding quantum planning into governance systems requires strategic alignment and regulatory foresight.
To be better positioned to respond to emerging requirements with agility and coherence. Enterprises must treat domains as strategic assets, not tactical checklists. Capability domains are not optional; they are foundational to disciplined execution.
From awareness to action
Quantum computing is no longer an abstract or future-facing concern. The vulnerabilities it introduces, particularly in cryptographic security, regulatory compliance and data trust, are already in motion. Threat actors are today harvesting encrypted data. They plan to decrypt it when quantum capabilities are feasible. That means sensitive information that is currently protected by classical encryption may already be compromised and is waiting for technological maturity to be exposed.
Regulators have recognised this risk. Governments are signalling that inaction by enterprises is no longer acceptable. The steps required to address these risks include cryptographic review, governance adaptation, capability building and structured planning. These measures can already be implemented with existing tools and guidance. Choosing to wait does not increase future options. It reduces them, forcing organizations into rushed and reactive decisions when external pressures intensify.
The consequences of inaction could be severe. Once scalable quantum decryption becomes operational, organizations without preparation may face regulatory penalties, legal exposure, reputational damage and operational disruption. The cost of recovery will far exceed the cost of timely preparation. Quantum readiness must be prioritized on equal terms with cybersecurity, regulatory compliance and business continuity.
This is not a call for the rushed adoption of quantum technologies. It is a call to build institutional awareness, structural agility and forward-planning capacity. Enterprise leaders must act with urgency. They should assign ownership, establish a clear roadmap, develop critical capabilities and engage with external partners and standards bodies. Those who act now will manage risk and retain strategic control. Those who wait may lose both. The data harvest has already begun. The time to act is now.
This article is published as part of the Foundry Expert Contributor Network.
Want to join?
Read More from This Article: How enterprise leaders should prepare for the quantum future
Source: News

