Ransomware remains one of the most persistent threats facing enterprises and public sector organizations. The latest research from ThreatLabz confirms that attacks are not only increasing in volume, but also shifting toward more targeted, data-driven extortion tactics.
The newly released Zscaler ThreatLabz 2025 Ransomware Report examines year-over-year spikes in ransomware activity blocked by the Zscaler cloud and a significant rise in public extortion cases. Together, these findings point to a critical reality: today’s ransomware threat landscape demands a new level of operational vigilance and a fundamentally different security architecture than traditional security models provide.
This blog post highlights select insights from the report. For the full analysis—including attack trends, threat actor profiles, and security guidance—download the ThreatLabz 2025 Ransomware Report.
5 key ransomware findings
ThreatLabz researchers analyzed ransomware activity from April 2024 to April 2025, looking at public data leak sites, Zscaler’s proprietary threat intelligence, ransomware samples, attack data, and telemetry from the Zscaler Zero Trust Exchange. Here are five important takeaways from this year’s report:
1. Ransomware attacks skyrocketed 145.9% year-over-year: This dramatic growth makes it clear that attackers are scaling campaigns faster than ever, with Zscaler blocking an unprecedented number of ransomware attacks over the past year.
2. Public extortion cases increased 70.1%: Far more organizations were listed on ransomware leak sites year-over-year as attackers escalate pressure tactics.
3. Data exfiltration volumes surged 92.7%: ThreatLabz analyzed 10 major ransomware families, uncovering a total of 238.5 TB of data exfiltrated—evidence that data theft is fueling extortion campaigns.
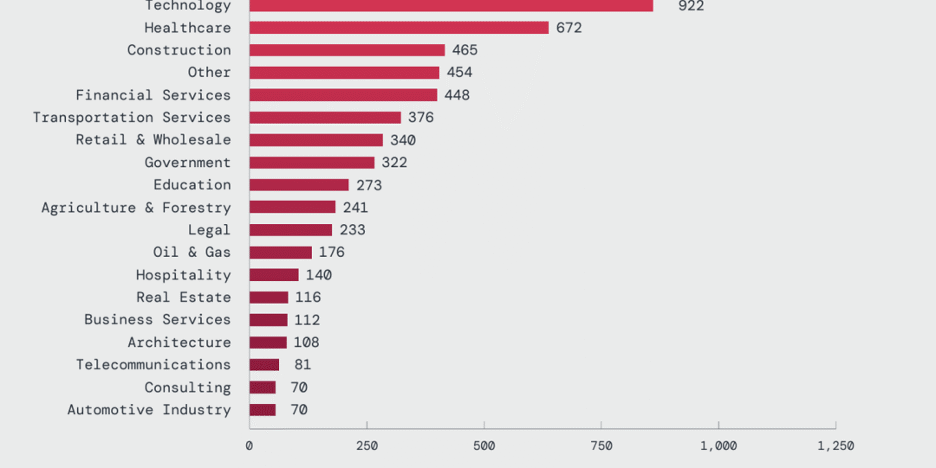
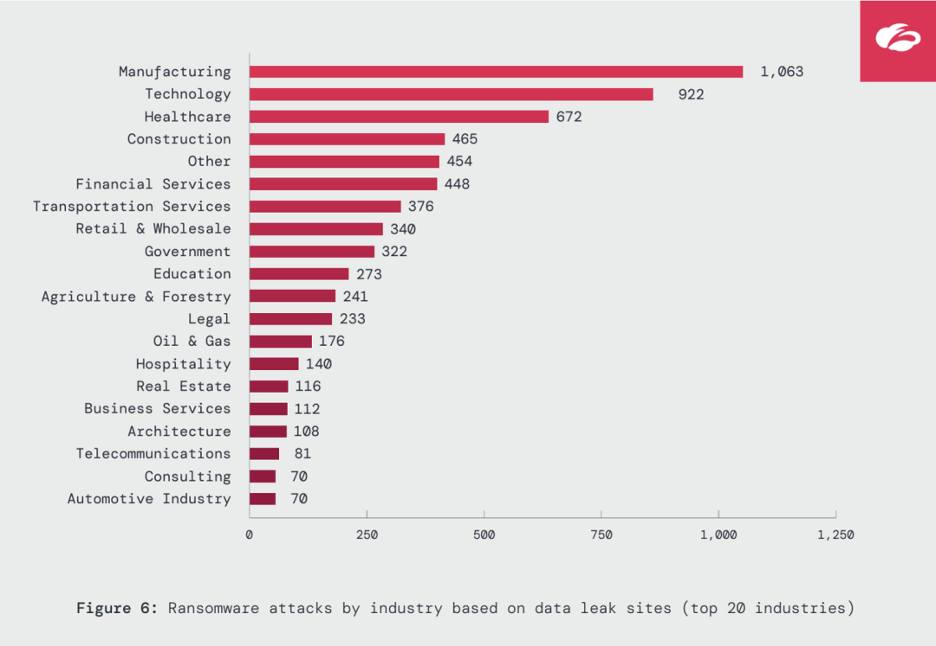
4. Critical industries continue to be prime targets: Manufacturing, Technology, and Healthcare experienced the highest number of ransomware attacks, while sectors like Oil & Gas (+935%) and Government (+235%) saw notable year-over-year spikes.
Zscaler
5. Ransomware groups are evolving fast: Established families like RansomHub, Clop, and Akira remained dominant, while 34 new groups emerged as identified by ThreatLabz—including rebrands or offshoots of defunct groups and new groups looking to fill the void left by takedowns or other disruptions. Collectively, they reflect a dynamic, fast-moving ransomware ecosystem where threat actors continually adapt.
Now trending: extortion over encryption, GenAI usage, and strategic targets
The ThreatLabz 2025 Ransomware Report covers several defining trends in how ransomware attacks are executed today:
- In many cases, data extortion is the priority. Some attackers are skipping file encryption altogether, opting to steal sensitive data and use the threat of public exposure via leak sites. These campaigns hook onto the threat of reputational damage, regulatory violations, and loss of intellectual property to pressure victims to pay even when their data isn’t encrypted.
- Generative AI is accelerating ransomware operations. ThreatLabz uncovered evidence of how one notorious threat group used ChatGPT to support the execution of its attacks. GenAI enables attackers to automate key tasks and write code to streamline operations and improve their attacks’ effectiveness.
- Targeting is more personalized. Ransomware threat actors have largely shifted away from traditional large-scale spam campaigns that are opportunistic in favor of more tailored attacks that impersonate IT staff to target employees with privileged access.
Read the full report for deeper insights into these trends.
Ransomware groups behind the surge
The report also offers a detailed look at threat groups driving the recent escalation in attacks. Among the most prolific over the past year were RansomHub, Clop, and Akira, responsible for a large share of leak site victims.
ThreatLabz researchers also identified the top five ransomware groups to watch over the next year—families that exemplify how ransomware is becoming more scalable and focused on extortion outcomes.
Tactics vary widely across groups. ThreatLabz observed strategies such as:
- Stealthy data theft that avoids disrupting business continuity
- Affiliate-driven Ransomware-as-a-Service campaigns using shared infrastructure, tools, and services
- Ransom demands that exploit regulatory violations to intensify pressure on victims
Vulnerabilities remain the easy way in
A constant and defining theme in ransomware attacks is the role of vulnerabilities as direct pathways to initial compromise. Widely-used enterprise technologies—including VPNs, file transfer applications, remote access tools, virtualization software, and backup platforms—continue to be weaponized by ransomware operators.
The report details examples of several major vulnerabilities exploited in ransomware campaigns over the past year. In most cases, attackers gained initial access through simple scanning and automated exploitation of internet-connected systems. This reinforces a hard truth: traditional defenses like firewalls and VPNs leave too much exposed, creating ideal conditions for lateral movement, data theft, and ransomware deployment.
Zero trust: the standard for stopping ransomware
As ransomware groups continue to evolve their playbooks—targeting sensitive data and exploiting reputational and regulatory pressure to strengthen their extortion leverage—defending against these attacks requires a comprehensive, proactive approach. This is exactly what a zero trust architecture delivers, eliminating the very conditions ransomware threat actors rely on: discoverable infrastructure, overly permissive access, and uninspected data flows.
The Zscaler Zero Trust Exchange delivers protection at every stage of the ransomware attack chain, including:
- Minimize exposure: The Zero Trust Exchange makes users, devices, and applications invisible from the internet—no public IPs, no exposed networks. This eliminates the attack surface during the earliest reconnaissance phase and dramatically reduces risk.
- Prevent initial compromise: Inline inspection of all traffic, including encrypted TLS/SSL traffic, at scale stops threats before they can cause damage. AI-driven browser isolation and cloud sandboxing add multiple layers of defense to neutralize zero-days and advanced threats—powered by advanced threat intelligence from ThreatLabz.
- Eliminate lateral movement: App-to-app and user-to-app segmentation enforces least-privilege access and eliminates the network from the equation, removing the paths ransomware operators rely on to spread. Integrated deception technology further disrupts attacks with decoys and false user paths.
- Block data exfiltration: Since today’s ransomware groups are just as (if not more) focused on stealing sensitive data as encrypting it, Zscaler’s unmatched inspection, AI-powered data classification, inline data loss prevention (DLP), and browser isolation are essential to prevent unauthorized data transfers and ensure sensitive data never leaves the organization.
With a zero trust architecture in place, organizations can control what users access, how data moves, and how resources are protected—effectively shutting down the pathways ransomware depends on and reducing risk at every stage of an attack.
Download the report—stay informed and prepared
The ThreatLabz 2025 Ransomware Report gives you the latest, data-backed view into the evolving ransomware landscape. Beyond the findings covered in this blog post, the full report explores the most targeted countries, provides front-line intelligence on other notable threat actor developments, and explains how ThreatLabz is supporting broader efforts to turn the tide against ransomware. It also outlines more detailed guidance to help strengthen defenses and build resilience against today’s ransomware threats.
Join our webinar this Tuesday, August 5 (EMEA, APAC) for a deeper dive and first-hand insights: ThreatLabz 2025 Ransomware Report: What’s Behind the Latest Surge in Attacks.
Get your copy of the full report today to stay informed and prepared with the latest ransomware threat research.
Read More from This Article: Ransomware surges, extortion escalates
Source: News