Cyber vulnerabilities are among a CIO’s greatest fears. And with good reason. No industry or organization is immune to the growing frequency, sophistication and success of cyberattacks and the steep, often devastating, organizational costs they incur. Yet, after collectively investing an estimated $219B1 worldwide in cybersecurity, only four in 10 organizational leaders feel confident that security is embedded in their technology and applications according to the Dell Technologies Innovation Index.
The answer lies in adopting a Zero Trust security framework, which is a security model that assumes no user or device should be automatically trusted based solely on their physical or network location. However, there is a lack of clarity in how to implement a comprehensive Zero Trust solution. As a result, many organizations are taking a self-defined, ad hoc approach to Zero Trust, using a collection of single-purpose solutions. This approach does not scale and often introduces additional vulnerabilities.
Instead, organizations need a holistic approach with validated Zero Trust as the goal. A validated approach implements the U.S. Department of Defense’s (DoD) Zero Trust reference architecture2 and is thoroughly tested to pass its stringent requirements—before adoption. Dell Technologies Project Fort Zero3 is doing just that, removing the burden of integration for organizations while reducing4 organizations’ time to Zero Trust deployment. Why the DoD’s Zero Trust strategy? The DoD is one of the world’s leading experts in data security and today its framework serves as the gold standard and default baseline for Zero Trust.
What is validated Zero Trust?
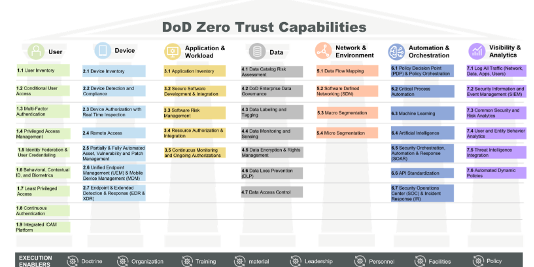
As depicted in Figure 1, the DoD developed an implementation roadmap5 by breaking down the seven pillars of the Zero Trust reference architecture into 45 capabilities. Each capability is further divided and organized into 152 Zero Trust activities.
Target Level Zero Trust includes meeting the minimum set of 91 activities to help secure and protect the enterprise while managing risks from currently known threats. Once an enterprise reaches the Target Level, it can move to Advanced Level Zero Trust. Advancedcapabilities include the complete set of 152 activities that enable adaptive responses to cybersecurity risks and threats while offering the highest level of protection.
The 152 activities are realized by mapping to over 1000 National Institute of Standards and Technology (NIST) security controls6 Only a system that complies with all applicable controls mapped to their respective activities can be considered a validated Zero Trust solution.
Title: “The US DoD’s Zero Trust Pillars and Capabilities” and hyperlink citation HERE.

Why is validated Zero Trust so secure?
As a concept, Zero Trust has been around for a while. Yet, since its inception, most organizations have pursued an ad hoc approach toward its implementation that targets typically only one of the seven essential Zero Trust pillars—usually the user. This partial solution may introduce more cyber risk because it makes it more convenient for hackers to attack the entire enterprise. An organization must protect the data and automate the threat response first.
In contrast, validated Zero Trust operates under the assumption that adversaries have already infiltrated the system. It emphasizes integration across all seven pillars, creating multiple policy checkpoints and automatically granting or denying requests based on user behavior patterns.
What is Project Fort Zero?
To help accelerate organizations’ path to validated Zero Trust, Dell launched Project Fort Zero, which will deliver a fully configured end-to-end Advanced Zero Trust solution validated by the U.S. DoD. That means a government assessment team will evaluate the Project Fort Zero solution for advanced maturity accreditation (for the full 152 activities and across all pillars) and certified compliance.
With this initiative, Dell has taken on the technology integration and orchestration, a burden that typically falls to individual organizations, by assembling more than 30 partners. As a result, Project Fort Zero will lower the barriers to Zero Trust adoption, reduce adoption time and enable organizations to make validated Zero Trust a reality and advance protection against cyberattacks.
Faced with the rising tide and sophistication of cyberattacks, organizations need the power of a security solution created and validated by a global security authority. With Project Fort Zero, Dell is making that very complex task an easy-to-adopt solution for organizations.
The time to accelerate to a new security approach is now
IT infrastructure has changed, and is growing in diversity, location/sprawl and size—all of which necessitates a new approach to secure it.
Getting started on the Zero Trust journey may be confusing, complex and challenging. But Project Fort Zero will help by teeing up a validated solution, aligning with emerging infrastructure needs and serving a variety of use cases such as on-premises data centers, remote or regional locations and in the field.
And as hackers’ levels of sophistication grow and scale, so too will the Dell validated Zero Trust solution. That way, we can help ease one of a CIO’s greatest fears by knowing their organizations are as secure and protected as possible.
Learn about Project Fort Zero
Discover how Zero Trust can help your organization
Read about the value of a validated Zero Trust solution
[2] https://dodcio.defense.gov/Portals/0/Documents/Library/(U)ZT_RA_v2.0(U)_Sep22.pdf
[3] https://www.dell.com/en-us/dt/solutions/zero-trust/index.htm
[4] https://dodcio.defense.gov/Portals/0/Documents/Library/ZTCapabilityExecutionRoadmap.pdf
[5] https://dodcio.defense.gov/Portals/0/Documents/Library/DoD-ZTExecutionRoadmap.pdf[1] https://csrc.nist.gov/pubs/sp/800/53/r5/upd1/final
Zero Trust
Read More from This Article: CIOs must safeguard organizations with a validated Zero Trust solution
Source: News